How to convert .pem file to .key file ?
This tutorial guides you on how to convert .pem file to .key file. I had generated keypair using OpenSSL instructions. It resulted in generating keypair in .pem file format. If you would like to convert .pem format to .key format then follow this.
Convert .pem file to .key file
The following command worked for me for converting private.pem file to private.key file
> openssl rsa -in private.pem -out private.key writing RSA key
Note, I have generated RSA private key, 2048 bit long using the following command.
> openssl genrsa -out private.pem 2048 Generating RSA private key, 2048 bit long modulus (2 primes) ..........................+++++ ...........+++++ e is 65537 (0x010001)
And if you want to generate DER encoded version of your private.pem private key the run the following command.
> openssl rsa -outform der -in private.pem -out private.key writing RSA key
Verify converted RSA private.key from private.pem
You need to run the following command to see all parts of private.key file. You would see content that got printed in the screen that includes the modulus, public exponent, private exponent, primes, exponents etc., which were used to perform RSA operations to generate RSA key as shown below.
>openssl rsa -text -in private.key
RSA Private-Key: (2048 bit, 2 primes)
modulus:
00:c3:01:79:16:a3:59:49:e1:95:15:98:85:4e:78:
74:21:d2:0c:ab:19:dc:fa:7b:5d:6e:a9:af:6b:13:
--
publicExponent: 65537 (0x10001)
privateExponent:
00:aa:75:34:2a:a4:b9:1d:0a:d2:2d:e1:77:cd:83:
1f:48:9c:fa:b3:e9:d4:af:23:7d:25:89:b0:2b:f1:
--
prime1:
00:ff:ad:b7:ab:09:3c:c0:f9:83:03:70:0d:89:59:
95:f5:3b:f6:62:b1:06:03:cc:44:36:34:2b:6a:61:
--
prime2:
00:c3:40:3a:d4:59:31:85:08:02:15:11:79:63:7c:
a8:cc:6c:f9:30:01:0f:12:53:f4:a9:42:2a:39:5f:
--
exponent1:
00:84:b6:c5:59:90:67:ea:bb:19:18:55:b7:91:0d:
e1:5a:f4:0f:06:57:61:09:e3:a3:9c:87:23:ea:0a:
--
exponent2:
78:7f:a5:4e:f4:14:e9:a2:fd:95:ff:08:c9:6b:5f:
c9:79:df:77:ce:cf:7c:62:2f:f6:5d:8d:2d:87:99:
--
coefficient:
00:db:49:af:cd:ac:10:7a:30:da:e9:89:d3:07:0a:
cd:52:c9:17:6f:ae:4c:34:1b:0a:63:26:61:a1:5d:
--
writing RSA key
-----BEGIN RSA PRIVATE KEY-----
MIIEpQIBAAKCAQEAwwF5FqNZSeGVFZiFTnh0IdIMqxnc+ntdbqmvaxNrpLUgmEHy
Kuk+UNWdNDlK5+ZkT9px9dUTmECQ6T8Q6javaUMSQbdvHDTH+Q6dfF7h2LRp/SjQ
C1jtzB1ynN8tNoTB+SoEbY3JDXhjY8bqplJjMwSTcMdUdZx3emFhZDglVvGRkkl7
7Zu/KzCl7Cx2uxcG+gp1EtW7X9+jankVWhr8reCvyX0ACaXzO6MncM0UIZ649cXw
t6KK5eL9vhDS6adAvS2C/KlnD0VPSLpd+hwBoA3g0skuMICIe42ljNU6dzgIPJKE
WEkljPT2do/plenwsrIRcQMZia7coqge5KwIPwIDAQABAoIBAQCqdTQqpLkdCtIt
4XfNgx9InPqz6dSvI30libAr8frrK+UFEsgj2GS/diqHhvlCQrM21iU9lXceZHoH
WTho80pbweRIi5bVWhHfVHY3TB0xN2tafv10ndSn0qnoFHHKMTv5mE/sj77KRozi
n/NnVace5oYXVDYw5IfP8yWV3DpPhynjn6H76tD5qtrf+TnTT3UwE0cE+gC45gZt
9zmJo/htfXDodSkp3jTZ1ThNpUHZkXXoLJoq/3YZMzvwkQHu5Sbfs/1NQb4wb6Zu
u/KZXGrEEIHtDDB2A95c+e1sSEcGCUURGWZ9t+V+JTFK5zgEkpNZ9Bs/pzgq6xpR
NGHFMlDxAoGBAP+tt6sJPMD5gwNwDYlZlfU79mKxBgPMRDY0K2ph92aS0StZlKJk
Bezi5nSrS3ijQsJDjFSQFxs+ufxb9dHTI9FkfHj1UbKAKmgnAroiUHkwgjZn/itT
+LIDm/qJz60iCBoMknvaMDdDQ+5MpTBAJfBtg/Mse1YqcdsRgkrR4/VXAoGBAMNA
OtRZMYUIAhUReWN8qMxs+TABDxJT9KlCKjlf9WyRG2uVIJ2JRz7vF3LZ91DhSVqP
e52z0vwI+824naZVPrqy45N0URk5qMWrDG/lpwpu7qAuaTqKdyZcc3uWtufT20Gq
iPc72w9yFM/pNRoQ54OuA7M+JHW8d9lqAe1AhwtZAoGBAIS2xVmQZ+q7GRhVt5EN
4Vr0DwZXYQnjo5yHI+oKhALIPq7DxvUr+i9l772rlHdAN0zjBxp12KiZvKyTh1us
vzDXegzHOervwBNj/HRlj2P4m/5lqHcRFUxBt1sq4ZO60H3E/Nww+0oULlSpkC0l
fwv3rMAy3KpzSbousnTn0e3tAoGAeH+lTvQU6aL9lf8IyWtfyXnfd87PfGIv9l2N
LYeZMX2ETKrmTBMy0xY/hHQce9/to2Q1yCf4p+7raBTtxn+JjTNl29THUCgTjpp3
vH8gzgGUZ2r9KlHWIuifpMBo9T38bNRQXzSjhy7CxWWJjiKsnsnAItjRK5A67wTL
V56hOVECgYEA20mvzawQejDa6YnTBwrNUskXb65MNBsKYyZhoV3r77uqsHEi3Fur
uvNaBanN9gz06IMKC0XbkH7QSCOxfjORJzurkqGzWGU6NowUCQ/MSPzgOQpBUoKZ
RoesCiTJgh9lkFlMjDPcBUZvvoJp6qHkPAEgsUr6KBHDYkaH898VnPA=
-----END RSA PRIVATE KEY-----
That’s it. Hope it helped 🙂
Also See:
- Get modulus and exponent for RSA public key ?
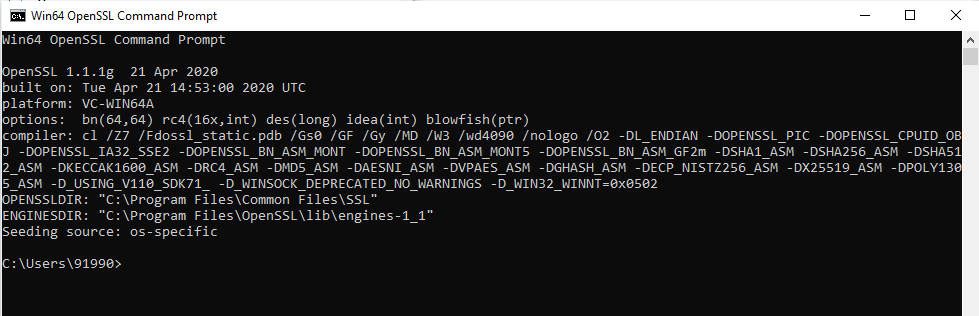
- How to install OpenSSL in Windows 10 64-bit Operating System ?
- Visual Studio Code Windows install location and Path issues from Terminal
- McAfee Agent cannot be removed while it is in managed mode
- Fix iPhone touch screen unresponsiveness
- How to add add 16GB RAM along with 8GB RAM – Acer Aspire 7 Laptop ?
- Generate public key and private key with OpenSSL in Windows 10
- How do I convert a PEM file to XML RSA key ?
- Guide to upload ISO image file to VMware ESXi datastores.
- Guide to install Operating System in the VMware ESXi server using vSphere Client.
- Read RSA Private Key Java: algid parse error, not a sequence
- How to read .pem file to get public and private keys ?
- Create JWT Token and Sign with RSA Private Key
- Java: Convert String to RSA Public Key
- Retrieve the Public Key from RSA Private Key ?